Cybersecurity & Privacy
Cybersecurity And Data Privacy: The Best Practices Unveiled

In today’s digital age, cybersecurity and data privacy are critical concerns. Protecting your information is more important than ever.
With cyber threats on the rise, understanding the best practices for cybersecurity and data privacy can save you from potential harm. This blog post will explore the most effective methods to safeguard your digital world. From strong passwords to secure networks, we will cover essential steps to keep your data safe.
By following these guidelines, you can reduce the risk of cyberattacks and ensure your personal information remains private. Stay informed and proactive about your cybersecurity and data privacy to protect yourself in the digital realm.
Credit: blogs.duanemorris.com
Introduction To Cybersecurity
In our digital world, cybersecurity is more crucial than ever. Cybersecurity involves protecting computers, servers, and networks from malicious attacks. It ensures the safety of our data and privacy.
Importance In The Digital Age
The digital age has revolutionized the way we live and work. With this change, the importance of cybersecurity has grown significantly. Here’s why:
- Protection of Personal Data: Our personal information is valuable. Cybersecurity helps keep it safe from hackers.
- Maintaining Privacy: Cybersecurity ensures our online activities remain private.
- Business Integrity: Companies rely on cybersecurity to protect sensitive information and operations.
- Preventing Financial Loss: Cyber attacks can lead to significant financial losses. Proper measures prevent this.
Common Threats
Understanding common cybersecurity threats is the first step in prevention. Some of the most frequent threats include:
- Phishing: Fraudulent attempts to obtain sensitive information by disguising as a trustworthy entity.
- Malware: Malicious software designed to damage or disable computers and systems.
- Ransomware: A type of malware that threatens to publish personal data or block access until a ransom is paid.
- DDoS Attacks: Distributed Denial of Service attacks overwhelm a system with traffic, causing it to crash.
- Man-in-the-Middle Attacks: Eavesdropping on communication between two parties to steal or alter information.
Each of these threats poses unique challenges. Staying informed and vigilant is key to maintaining cybersecurity.
| Threat | Description |
|---|---|
| Phishing | Attempts to trick users into providing sensitive data. |
| Malware | Software intended to harm or exploit any device. |
| Ransomware | Holds data hostage until a ransom is paid. |
| DDoS Attacks | Floods a network with traffic to crash it. |
| Man-in-the-Middle | Intercepts communication between two systems. |
By understanding these threats, we can better protect our digital lives. Implementing strong cybersecurity practices is essential for everyone in the digital age.
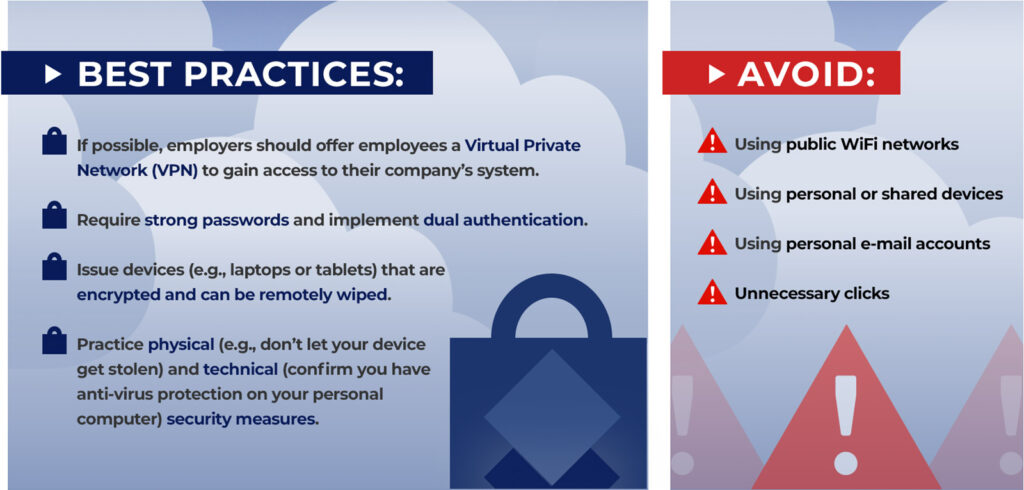
Credit: www.ruderware.com
Understanding Data Privacy
Understanding data privacy is essential in today’s digital world. Data privacy refers to the handling, storing, and sharing of personal information. This includes keeping sensitive data secure from unauthorized access. Let’s dive into some key aspects of data privacy.
Personal Data Protection
Personal data protection means safeguarding information that can identify an individual. This includes names, addresses, phone numbers, and email addresses. Protecting this data helps prevent identity theft and fraud. Regularly updating passwords and using encryption can enhance protection.
Organizations must implement security measures to protect personal data. This includes firewalls, antivirus software, and secure servers. Employees should be trained in data protection practices. This ensures they handle sensitive information properly.
Legal Implications
Laws and regulations govern how personal data is collected and used. Violating these laws can result in severe penalties. The General Data Protection Regulation (GDPR) is a key example. It applies to companies operating within the European Union.
Businesses must comply with data privacy laws to avoid fines. They should also inform users about data collection practices. Transparency builds trust and ensures legal compliance. Staying updated on changing laws is crucial for ongoing compliance.
Best Practices For Cybersecurity
In today’s digital age, cybersecurity is essential. Protecting your data from cyber threats can save you from potential harm. Implementing best practices is key to securing your digital environment. Let’s explore some of the best practices for cybersecurity.
Regular Software Updates
Always keep your software updated. Updates often contain security patches. These patches fix vulnerabilities. Without updates, you leave your system open to attacks. Set your software to update automatically if possible. This ensures you always have the latest security measures in place.
Strong Password Policies
Use strong passwords. Weak passwords are easy to guess. Create passwords with a mix of letters, numbers, and symbols. Change your passwords regularly. Do not use the same password for multiple accounts. Consider using a password manager. It can help you generate and store complex passwords safely.

Credit: cowbell.insure
Data Privacy Measures
Data privacy measures are essential for protecting sensitive information. These measures help ensure personal data stays private and secure. By following best practices, you can minimize the risk of data breaches and unauthorized access.
Encryption Techniques
Encryption techniques are crucial for data privacy. Encryption converts data into a coded format. Only authorized users can decode it. This makes it difficult for hackers to access sensitive information. Use strong encryption methods to protect data in transit and at rest. Common methods include AES and RSA. Regularly update encryption protocols to stay ahead of threats.
Data Anonymization
Data anonymization helps protect individual identities. Anonymization removes or modifies personal identifiers. This makes it hard to trace data back to individuals. Use techniques like data masking and pseudonymization. These methods safeguard privacy while allowing data analysis. Anonymization is vital for sharing data without exposing personal details.
Role Of Employees
Employees are the backbone of any organization’s cybersecurity strategy. Their actions and awareness can significantly impact the security posture of the company. By understanding their role and responsibilities, employees can help protect sensitive data and prevent cyber threats. Here we discuss two critical areas: Training Programs and Access Control.
Training Programs
Effective training programs are essential for building a security-conscious workforce. They should cover basic and advanced cybersecurity practices. These programs educate employees on recognizing phishing attempts, safe browsing habits, and proper data handling techniques.
- Conduct regular cybersecurity training sessions.
- Use real-world scenarios to illustrate potential threats.
- Provide updates on the latest cyber threats and trends.
- Evaluate employee understanding through quizzes and assessments.
Training should be continuous. It ensures that employees stay updated on new threats and best practices. This proactive approach reduces the risk of security breaches caused by human error.
Access Control
Access control is a crucial aspect of cybersecurity. It involves regulating who can view or use resources within an organization. Proper access control mechanisms limit exposure to sensitive information and reduce the risk of unauthorized access.
| Access Control Measure | Description |
|---|---|
| Role-based Access Control (RBAC) | Grants access based on job roles and responsibilities. |
| Multi-factor Authentication (MFA) | Requires multiple forms of verification for access. |
| Least Privilege Principle | Grants minimal access necessary for job functions. |
| Regular Access Reviews | Periodically check and update access permissions. |
Implementing strict access control measures ensures that only authorized personnel can access sensitive data. This reduces the chances of data breaches and enhances overall security.
Incident Response Planning
Incident response planning is crucial for cybersecurity and data privacy. It prepares organizations to handle data breaches and cyber-attacks efficiently. A well-structured plan minimizes damage and speeds up recovery. Let’s dive into key elements of incident response planning.
Detection And Containment
Early detection of security incidents is vital. Implement monitoring systems to identify threats quickly. Use firewalls, antivirus, and intrusion detection systems. Train staff to recognize suspicious activities. Quick detection helps in minimizing damage.
Once detected, contain the threat. Isolate affected systems to prevent spread. Disconnect compromised devices from the network. Limit access to sensitive data. Containment buys time to analyze and mitigate the threat.
Recovery Strategies
After containment, focus on recovery. Restore affected systems from clean backups. Ensure backups are recent and secure. Verify the integrity of restored data. This step is critical to resume normal operations.
Develop a communication plan. Inform stakeholders about the incident and recovery steps. Transparency builds trust and maintains credibility. Regularly update them on progress and any further steps.
Review and update your incident response plan. Learn from the incident and improve your strategies. Regular drills and training keep the team prepared. Stay vigilant and ready for future threats.
Emerging Technologies
Technology is evolving rapidly. Cybersecurity and data privacy must adapt. Emerging technologies play a crucial role in this evolution. These technologies help protect sensitive information and safeguard digital assets. Let’s explore two key areas: AI in cybersecurity and blockchain for data privacy.
Ai In Cybersecurity
Artificial Intelligence (AI) is a powerful tool. It helps identify and respond to threats quickly. AI systems analyze data and detect patterns. These patterns can indicate potential security risks. This allows for faster and more accurate threat detection.
AI can also automate many security tasks. This reduces the workload for human security teams. They can focus on more complex issues. AI can help with:
- Intrusion detection
- Malware analysis
- Behavioral analytics
AI systems learn from past data. They continuously improve over time. This makes them more effective at preventing cyberattacks. Machine learning and deep learning are key components of AI. These technologies help AI systems become smarter and more efficient.
Blockchain For Data Privacy
Blockchain technology is known for its security. It provides a decentralized way to store data. Each block in the chain is linked to the previous one. This makes it difficult for attackers to alter data.
Blockchain offers several advantages for data privacy:
| Feature | Benefit |
|---|---|
| Decentralization | Reduces single points of failure |
| Transparency | Increases data traceability |
| Immutability | Prevents data tampering |
Blockchain can be used in various sectors. It is useful in finance, healthcare, and supply chain management. It ensures data integrity and enhances privacy. Smart contracts are another feature of blockchain. They automate and enforce rules without human intervention.
Both AI and blockchain are reshaping cybersecurity and data privacy. These technologies offer new ways to protect sensitive information. By adopting these tools, organizations can stay ahead of emerging threats. Stay informed about the latest advancements to keep your data safe.
Future Trends
The world of cybersecurity and data privacy is ever-evolving. Future trends promise to bring new solutions and challenges. Businesses must stay informed and adapt to maintain security. Let’s explore some key trends shaping the future.
Predictive Analytics
Predictive analytics is becoming crucial in cybersecurity. It helps predict potential threats before they happen. By analyzing patterns, it can spot unusual activities. This allows businesses to act quickly and prevent breaches.
Key benefits of predictive analytics:
- Early threat detection
- Improved response times
- Reduced risk of data breaches
- Better resource allocation
Implementing predictive analytics involves using big data and AI. These tools analyze vast amounts of data in real-time. They identify patterns that indicate potential threats. This proactive approach is becoming essential for businesses.
Global Regulations
Global regulations are tightening around data privacy. Countries are introducing stricter laws to protect personal data. Businesses must comply with these laws to avoid heavy fines.
Some key regulations include:
| Regulation | Region |
|---|---|
| GDPR | Europe |
| CCPA | California, USA |
| PIPEDA | Canada |
Businesses must stay updated on these regulations. Compliance involves updating policies and systems. It ensures the protection of user data and builds trust.
Failure to comply can result in severe penalties. It can also damage a company’s reputation. Staying ahead of global regulations is crucial for business success.
Frequently Asked Questions
What Are The Best Practices For Cybersecurity?
Use strong passwords. Enable two-factor authentication. Keep software updated. Backup data regularly. Educate employees about threats.
How Can I Protect My Data Privacy Online?
Use secure passwords. Avoid sharing personal information. Use privacy settings on social media. Be cautious with public Wi-Fi.
Why Is Data Encryption Important?
Data encryption protects sensitive information. It prevents unauthorized access. It ensures data privacy and security.
How Often Should I Update My Software?
Update software regularly. Install patches as soon as they are available. This helps protect against vulnerabilities.
What Should I Do If My Data Is Breached?
Change passwords immediately. Notify affected parties. Monitor accounts for suspicious activity. Report to relevant authorities.
Conclusion
Implementing best practices in cybersecurity and data privacy protects your information. Regularly update your software and use strong passwords. Educate your team about common threats. Always back up your data. Use multi-factor authentication for added security. Keep personal and business data separate.
Monitor your systems for unusual activity. Secure your network with firewalls and antivirus programs. Stay informed about the latest cybersecurity trends. Remember, a proactive approach ensures better protection. Stay safe, stay secure.

-
Insurance3 years ago
Here Is How to Get Your Instant Car Insurance Online In The USA
-
Software as a Service-SaaS4 months ago
10 Essential SaaS Tools for Streamlining Your Business in 2024
-
Insurance3 years ago
Best Pet Insurance Companies & Plans
-
gadgets3 years ago
Get The New iPhone 13 For 2022.Harry up.
-
Make Money Online6 months ago
Maximizing Your Earnings With Online Survey Feedback: Top Tips
-
Finance & Accounting Software3 months ago
How Automated Expense Management Simplifies Your Financial Workflow Efficiently
-
Finance & Accounting Software4 months ago
Unlock Financial Clarity: How Contract Management Software Transforms Your Business
-
Make Money Online6 months ago
Creating Passive Income With Blogging: Step-By-Step Guide to Success